I’ve written a number of posts about security issues relating to the Internet and World Wide Web. We’re all at risk and it’s getting more difficult to keep up our defenses. According to the Ponemon Institute, a Tucson-based research firm, it costs a company over $200 to deal with each customer record that has been compromised when security systems are breached [“Data Breaches Are More Costly Than Ever,” by Brian Krebs,Washington Post, 3 February 2009]. The Institute examined 43 companies that reported breaches last year and they found that it cost an average of $6.6 million to mitigate the consequences of the breach. The study “measured the direct costs of a data breach, such as hiring forensic experts; notifying consumers; setting up telephone hotlines to field queries from concerned or affected customers; offering free credit monitoring subscriptions; and discounts for future products and services. The survey also sought to measure more intangible costs of a breach, such as the loss of business from increased customer turnover and decreases in consumer trust.” A year ago,BusinessWeekpublished an article that highlighted the “rising attacks on America’s most sensitive computer networks” [“The New E-spionage Threat,” by Brian Grow, Keith Epstein, and Chi-Chu Tschang,” 21 April 2008 print issue]. That article began with an interesting tale.
“The e-mail message addressed to a Booz Allen Hamilton executive was mundane—a shopping list sent over by the Pentagon of weaponry India wanted to buy. But the missive turned out to be a brilliant fake. Lurking beneath the description of aircraft, engines, and radar equipment was an insidious piece of computer code known as ‘Poison Ivy’ designed to suck sensitive data out of the $4 billion consulting firm’s computer network. The Pentagon hadn’t sent the e-mail at all. Its origin is unknown, but the message traveled through Korea on its way to Booz Allen. Its authors knew enough about the “sender” and “recipient” to craft a message unlikely to arouse suspicion. Had the Booz Allen executive clicked on the attachment, his every keystroke would have been reported back to a mysterious master at the Internet address cybersyndrome.3322.org, which is registered through an obscure company headquartered on the banks of China’s Yangtze River.”
Related articles by Zemanta
- Multivariable Testing and Analytics for Web CMS (digitalassetmanagement.org.uk)
- Armies of Agents – At Your Command (digitalassetmanagement.org.uk)
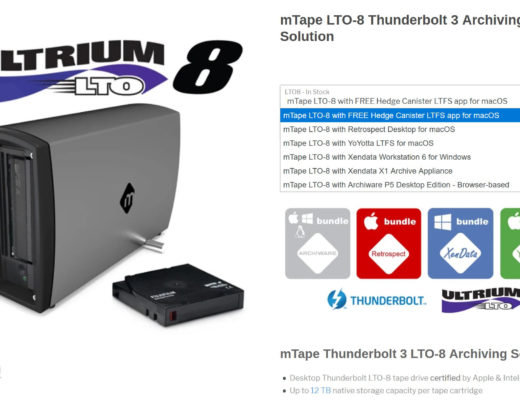
- Intelligent Archiving (digitalassetmanagement.org.uk)
Filmtools
Filmmakers go-to destination for pre-production, production & post production equipment!
Shop Now
![Time for a New Internet? 3 Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_c.png?x-id=cd391e5d-4f1b-45a6-a141-565e82f5b74b)